 [01]
[01]Discovery and Assessment
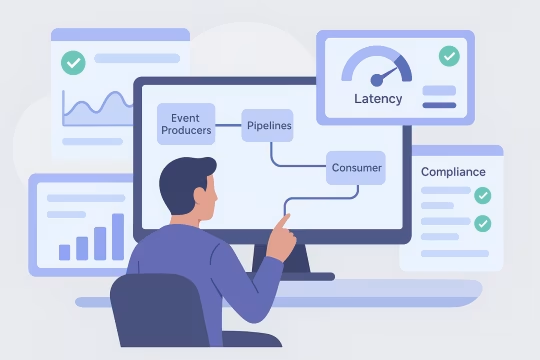
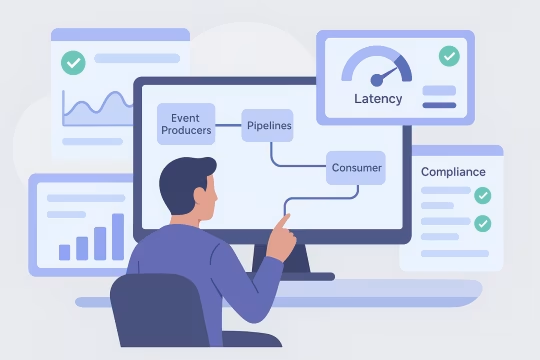
Map current event producers, pipelines, and consumers, including pain points and operational incidents. Capture non-functional requirements such as latency, volume, retention, and compliance constraints.
Event data platforms turn behavioral and operational signals into a dependable data product. This service focuses on event data platform architecture for CDP ecosystems: defining end-to-end patterns for event collection, real-time data ingestion, streaming, validation, storage, and consumption so events remain consistent as products, channels, and teams evolve.
Organizations need this when event tracking grows beyond a single application and becomes a shared dependency for analytics, experimentation, personalization, and compliance. Without a clear CDP event infrastructure design, teams ship events with inconsistent naming, unstable schemas, and unclear ownership, which makes downstream datasets brittle and expensive to maintain.
A well-defined enterprise event streaming architecture establishes contracts (schemas and versioning), ingestion patterns (streaming and batch), and operational controls (observability, replay, and access governance). The result is a platform that supports scalable delivery: teams can add or change events with controlled impact, data engineers can build reliable pipelines, and analytics teams can trust that metrics reflect consistent, validated inputs.
As digital platforms expand, event tracking often grows organically: multiple teams instrument different clients, naming conventions drift, and the same business concept is represented by several incompatible events. Collection endpoints and streaming topics proliferate without clear ownership, and downstream consumers depend on undocumented assumptions about payload shape and meaning.
These issues quickly become architectural. Without explicit schema contracts and versioning, small changes in a client release can break ingestion, corrupt derived tables, or silently shift metrics. Data engineers spend time building defensive transformations and backfills instead of improving the platform. Analytics teams lose confidence because dashboards disagree, attribution logic becomes inconsistent, and experimentation results are hard to reproduce.
Operationally, the platform becomes difficult to run. Incident response is slowed by limited lineage and weak observability across collectors, streams, and transformations. Reprocessing and replay are risky or impossible, retention policies are unclear, and privacy requirements are handled inconsistently across sources. Over time, the cost of change increases and the event ecosystem becomes a bottleneck for product delivery and data-driven decision-making.
Review current tracking sources, collectors, streams, and downstream datasets. Identify critical consumers, data contracts in use, failure modes, and operational constraints such as latency, retention, and privacy requirements.
Define event taxonomy aligned to business domains and product surfaces. Establish naming conventions, entity identifiers, and required context fields so events can be joined, attributed, and analyzed consistently across channels.
Design schema standards, validation rules, and versioning strategy. Specify compatibility rules, deprecation paths, and ownership so producers can evolve payloads without breaking consumers.
Define topics, partitions, ordering expectations, and replay strategy for event streams. Document ingestion patterns for high-volume clients, backpressure handling, and routing to multiple sinks when required.
Introduce validation at collection and ingestion layers, including schema enforcement, required fields, and anomaly detection. Specify quarantine and dead-letter patterns to prevent bad events from contaminating curated datasets.
Design metrics, logs, traces, and lineage mapping across collectors, streams, and transformations. Establish SLOs for ingestion latency, drop rates, and schema violations to support reliable operations.
Define access controls, retention policies, and privacy handling for event payloads. Align with data classification, consent signals, and audit requirements, including controlled access to raw versus curated datasets.
Create an incremental migration plan from current tracking to the target architecture. Prioritize high-impact domains, define cutover and backfill strategies, and establish ongoing governance for change management.
This service establishes the technical foundations needed to run event data as a platform capability rather than a collection of ad hoc pipelines. The focus is on CDP event infrastructure design with clear contracts, enterprise event streaming architecture, reliable replay, and operational controls that keep data consistent as producers and consumers change. The architecture emphasizes traceability from source instrumentation to curated datasets, with explicit governance for schema evolution, access, and retention.
Engagements follow a clear engineering sequence from discovery through target design, implementation support, and long-term evolution. We focus on the architectural decisions, contracts, and operating model behind Kafka event pipeline design and Snowplow event data platform implementations—reducing ambiguity while keeping the event ecosystem reliable and maintainable.
 [01]
[01]Map current event producers, pipelines, and consumers, including pain points and operational incidents. Capture non-functional requirements such as latency, volume, retention, and compliance constraints.
 [02]
[02]Define the reference architecture across collection, streaming, processing, and storage layers. Document key decisions, trade-offs, and interfaces between platform components and teams.
 [03]
[03]Produce the event taxonomy, schema standards, and versioning rules. Define ownership, review workflows, and compatibility expectations to support safe change over time.
 [04]
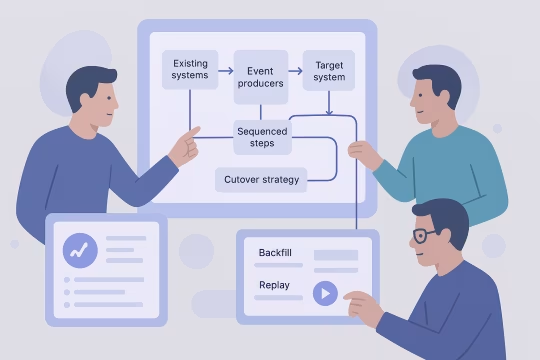
[04]Design how existing producers and datasets transition to the target model. Provide sequencing, cutover strategies, and backfill/replay approaches to minimize disruption to reporting and downstream systems.
 [05]
[05]Specify monitoring, alerting, runbooks, and SLOs for collectors, streams, and transformations. Define incident response patterns, replay procedures, and capacity planning inputs.
 [06]
[06]Establish governance processes for schema changes, access requests, and retention updates. Align stakeholders across product, data, and security to ensure decisions are enforceable and auditable.
 [07]
[07]Support teams during build-out with architecture reviews, PR feedback, and integration troubleshooting. Validate that the implemented system matches the intended contracts and operational model.
 [08]
[08]Introduce a cadence for reviewing event health, schema drift, and consumer needs. Maintain a backlog of platform improvements and refine standards as the ecosystem grows.
A stable event data platform reduces the cost of change and improves confidence in analytics outputs. The impact comes from fewer breaking changes in enterprise event streaming, faster diagnosis of data issues through data quality and observability, and a clearer operating model for teams producing and consuming event data.
Consistent schemas and validation reduce silent data drift and conflicting definitions. Analytics teams can trust that dashboards and experiments reflect stable inputs across releases and channels.
Clear event standards and ownership reduce back-and-forth during implementation. Teams can add new tracking with predictable downstream behavior and fewer ad hoc transformations.
Replay strategies, dead-letter handling, and observability reduce the blast radius of failures. Incidents are easier to detect and resolve because lineage and SLOs make impact explicit.
Governed contracts and quality gates reduce the need for defensive pipeline logic and repeated cleanup work. Engineering time shifts from firefighting to platform improvements and new capabilities.
Topic strategy, partitioning, and capacity planning support growth in event volume and consumer count. The platform can scale without frequent redesign of ingestion and processing layers.
A shared taxonomy and change process reduces ambiguity between product, engineering, and analytics. Decisions about event meaning and evolution become explicit and reviewable.
Retention and access controls reduce uncontrolled exposure of sensitive payloads. Consent propagation and classification patterns make privacy requirements easier to implement consistently.
Adjacent services that extend event data platform architecture into CDP implementation, operations, governance, and downstream analytics delivery—especially where enterprise event streaming and schema governance must connect to activation and measurement use cases.
Enterprise CRM data synchronization and identity mapping
Event-driven journeys across channels and products
CDP audience activation with governed delivery to channels
Audience sync activation engineering for CDP activation
CDP real-time decisioning design for real-time experiences
Customer analytics platform implementation for governed metrics and behavioral analytics
Unified customer profile architecture and insight-ready datasets
Scalable enterprise audience segmentation models and cohort definition frameworks
Consistent experiment tracking, metrics, and attribution
Common questions from platform and data leaders evaluating event data platform architecture, including design decisions, operations, governance, and engagement expectations.
The choice is driven by consumer needs, operational maturity, and cost constraints rather than ideology. Streaming-first is appropriate when you have low-latency use cases (near-real-time dashboards, personalization, alerting) and the organization can operate always-on ingestion with clear SLOs. Batch-first can be the right starting point when most consumers are daily analytics, volumes are moderate, and the priority is consistent modeling and governance before introducing real-time complexity. In practice, many enterprise platforms adopt a hybrid: events are collected continuously, landed into a durable raw store, and then processed into curated datasets on a schedule, while a subset of events is also routed to streaming consumers. The architecture should make this an explicit design: define the canonical raw event record, the replay mechanism, and the contract boundaries so that adding streaming consumers later does not require re-instrumentation. We document the latency tiers, identify which datasets must be real time, and design ingestion and processing layers accordingly, including backpressure handling, retention, and reprocessing paths.
At enterprise scale, the goal is to make event changes predictable and reviewable. A good strategy defines: a canonical event envelope (shared fields like timestamps, identifiers, source, consent), domain-specific payloads, and explicit compatibility rules. Typically, adding optional fields is backward compatible, while changing types, renaming fields, or altering semantics requires a version bump and a deprecation plan. Versioning should be tied to governance, not just tooling. Teams need owners for each event domain, a review workflow for schema changes, and a published contract that downstream consumers can rely on. A schema registry can enforce structural validity, but you also need semantic rules (for example, what “revenue” means, currency handling, or how sessions are defined). We also recommend designing for coexistence: allow multiple schema versions to be ingested during migration windows, and ensure curated datasets can normalize versions into stable analytics tables without breaking existing reports.
Observability needs to cover three layers: ingestion health, data correctness, and consumer impact. For ingestion, we define metrics such as request rates, collector errors, queue depth, Kafka produce/consume lag, partition skew, and drop/quarantine rates. For correctness, we add schema violation counts, required-field failures, deduplication rates, and anomaly detection on key dimensions (for example, event volumes by source or product area). Consumer impact requires lineage and SLIs that map platform signals to datasets and dashboards. We define SLOs for end-to-end latency (event time to availability in curated tables), completeness (expected versus received volumes), and freshness. Alerts should be actionable: they must point to the failing component and the affected domains. We also design runbooks and replay procedures as part of observability. If you cannot safely reprocess a time window, you do not have a complete operational model for event data.
Replay and late data handling are architectural concerns that must be designed upfront. We start by defining the canonical raw event store and the immutable event record, including event time, ingestion time, and unique identifiers for deduplication. From there, we design processing so curated datasets can be rebuilt deterministically for a given time window. For streaming systems, we specify retention and compaction strategy, and we design replay paths that do not depend on fragile consumer offsets. For batch processing, we define incremental versus full rebuild patterns and how late events are merged. Common approaches include watermarking, partitioning by event time with controlled update windows, and idempotent upserts into curated tables. We also define operational controls: who can trigger a replay, what validation must pass before publishing rebuilt datasets, and how downstream consumers are notified. The objective is to make reprocessing routine and safe rather than an exceptional, high-risk activity.
Snowplow provides strong primitives for structured event collection and enrichment, but enterprise implementations often vary across products and historical setups. We integrate by first defining the desired event taxonomy and schema standards, then mapping existing Snowplow events and contexts to the target model. Where necessary, we introduce transitional enrichments or transformations to normalize legacy payloads. On the pipeline side, we design how Snowplow collectors and enrichments feed the streaming backbone and raw storage, and how curated datasets are produced for analytics. This includes decisions about where validation happens (collector, enrichment, stream processor, or warehouse), and how to route quarantined events for investigation. We also address operational integration: monitoring across Snowplow components, handling schema updates, and aligning ownership between product teams producing events and the data platform team operating the pipeline. The goal is to reduce custom per-team logic while keeping migration incremental.
Integration depends on latency requirements, transformation strategy, and governance. We typically define a raw landing zone that preserves the original event record and supports replay, then a curated layer optimized for analytics. Kafka-to-warehouse integration can be implemented via stream processing, connectors, or micro-batch ingestion, but the architecture must specify exactly-once expectations, deduplication keys, and how schema evolution is handled end to end. We also define how topics map to datasets: whether you use one topic per domain, per event type, or per producer, and how that impacts downstream table design and access control. Partitioning strategy must align with throughput and consumer parallelism, while also supporting predictable backfills. Finally, we design data contracts between streaming and analytics layers: what constitutes “published” curated data, how quality gates are enforced, and how changes are communicated to analytics consumers to avoid breaking reports.
Ownership should be aligned to domains, not to the data platform team alone. Product or platform teams typically own the meaning of events in their domain (what is emitted and why), while the data platform team owns the shared standards, tooling, and operational constraints. Analytics engineering often co-owns the curated model and ensures events are usable for reporting and experimentation. Change control is enforced through a lightweight but explicit workflow: proposed schema changes are reviewed against compatibility rules, required contexts, and privacy constraints. Approval gates can be implemented in CI for schema repositories, with automated validation and documentation generation. For high-impact domains, we recommend a change advisory cadence and clear deprecation timelines. The key is to make governance practical: fast enough to not block delivery, strict enough to prevent uncontrolled drift. We define roles, review criteria, and escalation paths, and we ensure the process is supported by tooling rather than manual policing.
Documentation stays accurate when it is generated from the same source of truth used to validate events. We recommend treating event schemas and taxonomy as code: stored in version control, reviewed via pull requests, and validated in CI. From that repository, documentation can be generated automatically, including field definitions, examples, ownership, and compatibility notes. Discoverability requires more than a wiki. We design how event definitions are indexed in a catalog, how they link to datasets and dashboards, and how lineage is exposed so users can answer: where does this metric come from, and which events feed it. We also define minimum documentation requirements for new events, such as business meaning, expected cardinality, and privacy classification. To keep it current, we add operational feedback loops: schema violation reports, unused event detection, and periodic reviews of high-change domains. This turns documentation into an operational asset rather than a static artifact.
Common failure modes include schema drift, silent drops, duplicate events, and consumer lag that causes partial datasets. Schema drift happens when producers change payloads without coordination; mitigation is contract enforcement, compatibility rules, and staged rollouts. Silent drops occur when collectors or pipelines reject events without visibility; mitigation is explicit quarantine paths, dead-letter queues, and alerting on drop rates. Duplicates and out-of-order events are frequent in distributed systems, especially with retries and mobile clients. Mitigation includes stable event identifiers, idempotent processing, and clear deduplication rules in curated datasets. Consumer lag and partition skew can create uneven processing and freshness issues; mitigation includes partition strategy, capacity planning, and SLO-based monitoring. Another risk is governance failure: too much friction leads teams to bypass standards, while too little control leads to chaos. We mitigate by designing a governance model that is enforceable via tooling and aligned to team responsibilities, with clear escalation for exceptions.
We start by classifying event fields and defining what should never be collected. The architecture should minimize sensitive payloads by design, using stable identifiers and controlled enrichment rather than embedding personal data in events. Consent signals should be treated as first-class context and propagated through ingestion and processing so downstream datasets can enforce usage rules. Access control is layered: raw events often require stricter permissions than curated datasets. We define retention policies per classification, audit requirements, and mechanisms for redaction or deletion where applicable. For streaming systems, we also consider how sensitive data is handled in topics, logs, and dead-letter flows, ensuring that operational tooling does not become an unintended exposure path. Finally, we define governance processes for approving new fields and contexts, including security and privacy review criteria. The goal is to make compliance operational: enforceable controls, clear ownership, and measurable adherence rather than informal guidelines.
Artifacts are designed to be directly actionable by engineering teams. Typically this includes a target reference architecture (collection, streaming, processing, storage, and consumption), a domain event taxonomy, and schema standards with versioning and compatibility rules. We also deliver topic and partitioning guidance, replay and backfill design, and quality gate patterns. On the operational side, we provide an observability plan with key metrics, SLOs, and alerting recommendations, plus runbooks for common incidents such as ingestion failures, schema violations, and replay requests. Governance artifacts include ownership mapping, change workflows, and documentation standards, often aligned to a schema-as-code repository structure. We also produce a migration roadmap: sequencing, dependencies, and risk controls for moving from current tracking to the target model without breaking reporting. If implementation support is included, we add architecture reviews and validation checkpoints to ensure the build matches the intended contracts and operating model.
We design the engagement to be incremental and compatible with existing reporting commitments. First, we identify critical datasets and dashboards that must remain stable, and we map which events and pipelines they depend on. That dependency map informs migration sequencing and the introduction of transitional normalization layers where needed. We also establish a change management approach: schema changes are staged, compatibility is enforced, and deprecations have explicit timelines. For high-risk areas, we recommend dual-writing or parallel pipelines during cutover windows, with validation comparing old and new outputs before switching consumers. Collaboration is structured around short feedback cycles with product instrumentation teams, data engineering, and analytics stakeholders. The goal is to improve the platform while keeping the current analytics supply chain functioning, using controlled rollouts, clear ownership, and measurable quality gates rather than large, disruptive rewrites.
Collaboration typically begins with a focused assessment to establish scope and constraints. We start with stakeholder interviews across data engineering, platform architecture, and analytics to understand current pain points, critical consumers, and non-functional requirements such as latency, retention, and privacy. In parallel, we review existing tracking plans, Snowplow or collector configurations, Kafka topology (if present), and representative downstream models. From that input, we define a problem statement and success criteria that are measurable: for example, reducing schema violations, improving dataset freshness, or enabling safe replay. We then agree on the depth of architecture work needed: a reference architecture only, or architecture plus migration planning and implementation support. The first tangible outputs are usually a current-state map, a prioritized set of architectural decisions to make, and a short roadmap for the next 4–8 weeks. This creates alignment before any large changes are introduced to instrumentation or pipelines.
These case studies showcase implementations of event data platform architecture, including schema governance, streaming patterns, and operational controls within CDP ecosystems. They provide real-world examples of scalable event ingestion, validation, and analytics delivery that align closely with the service's focus on reliable and evolvable event infrastructure design. The selected work highlights measurable outcomes in data quality, platform stability, and governance across complex enterprise environments.
These articles expand on the architecture and governance decisions that make event data platforms reliable in production. They cover schema evolution, consent enforcement, and ownership models that help keep tracking, activation, and analytics aligned as systems change.
Let’s review your current event ecosystem, identify architectural risks, and define a practical target architecture with clear contracts, observability, and an incremental migration plan.