In small Drupal implementations, editorial permissions often begin with a straightforward model. Authors create content. Editors review it. Publishers approve it. Administrators handle the rest.
That model works until the organization changes faster than the permission system does.
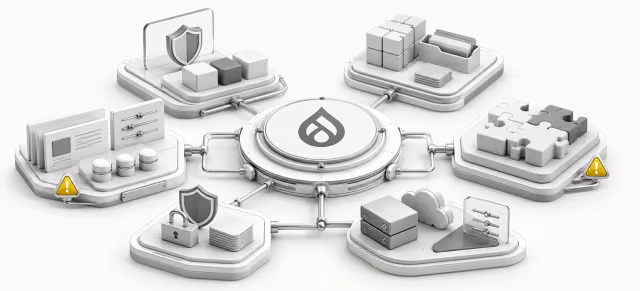
At enterprise scale, publishing rarely belongs to one team with one approval path. Regional teams need local control. Legal teams need selective review. Medical, regulatory, brand, or compliance stakeholders may need visibility into some content types but not others. Shared platform teams must keep delivery moving while also protecting production controls. Over time, what started as a clean role structure can turn into a patchwork of exceptions.
This is where Drupal editorial permissions architecture becomes a governance problem, not just a configuration problem. The real challenge is not assigning permissions one by one. It is designing a durable operating model that defines who can do what, on which content, under which approval conditions, and with what level of accountability.
Check your Drupal permissions and workflow risksRun a quick Drupal Platform Health CheckWhy simple Drupal role models stop working in enterprise publishing
Simple role models usually assume stable relationships between people, teams, and content. Enterprise publishing breaks that assumption in several ways.
First, business responsibility is rarely uniform. A global content team may own templates and standards, while country teams own market-specific copy. Product teams may control some sections of the site, but regulated content may still require legal or medical sign-off. A single "editor" role cannot capture those distinctions without becoming either too powerful or too restrictive.
Second, enterprise platforms often support multiple content domains at once. The same Drupal estate may host corporate communications, product marketing, support content, campaign landing pages, and policy material. Each domain can have a different risk profile. The permissions model has to reflect that difference.
Third, organizations change. Teams merge. Regions are added. Governance gets stricter after an audit. Platform consolidation brings previously separate sites into a shared model. If permissions were not designed as an architecture, every organizational change creates another exception.
That is how platforms end up with roles created for individual teams, temporary overrides that never disappear, and workflows that encode past compromises rather than current governance.
Signs of permission sprawl: exception roles, duplicated workflows, emergency admin access
Permission sprawl usually appears gradually. It is often rationalized as necessary flexibility, especially when delivery pressure is high. But the warning signs are fairly consistent.
Common indicators include:
- roles created for one region, one department, or one exceptional process
- overlapping roles with unclear differences in capability
- users assigned multiple roles to approximate the access they actually need
- workflow states duplicated because permissions could not support the intended review path
- emergency use of administrator access to unblock publishing
- weak separation between content approval rights and site administration rights
- limited confidence in who can publish what across environments or sites
These are not merely hygiene issues. They affect platform risk.
When teams cannot explain why a role exists, whether it is still needed, or what business control it represents, permissions stop being a reliable governance mechanism. They become an undocumented workaround layer.
In regulated or high-visibility publishing contexts, that creates obvious problems. Approval obligations can become inconsistent. Audit trails may show who changed content, but not whether the right governance path was followed. Least privilege becomes hard to enforce because broad access is often the quickest way to keep operations moving.
See where editorial controls break at scale
Assess role sprawl, approval gaps, and governance weaknesses across your Drupal publishing model.
- Audit role complexity
- Spot approval gaps
- Reduce admin overreach
Mapping business responsibilities to platform permissions
A better model starts outside Drupal.
Before defining roles or workflow states, platform teams should map business responsibilities. That means identifying the operational responsibilities that the system needs to support, not just the job titles currently in use.
Useful responsibility categories often include:
- content creation
- editorial revision
- structural review for content quality or standards
- business approval
- legal or compliance approval
- publication authorization
- taxonomy or shared content management
- platform configuration and release control
This distinction matters because job titles are inconsistent across organizations. One business unit's "editor" may only draft and revise. Another unit's "editor" may have publishing authority. A role model built directly from titles often becomes ambiguous immediately.
By contrast, a responsibility-based model creates clearer architecture. It asks questions such as:
- Which responsibilities must be separated for control reasons?
- Which responsibilities can be combined safely for low-risk content?
- Which responsibilities vary by content type, brand, region, or market?
- Which responsibilities require named accountability rather than general team access?
Once those responsibilities are clear, permissions can be designed to support them consistently. Drupal roles then become implementation vehicles for defined controls rather than containers for loosely grouped power.
Separating editorial capability, governance control, and technical administration
One of the most common enterprise mistakes is treating all elevated access as roughly equivalent. In practice, editorial capability, governance control, and technical administration serve very different purposes.
Editorial capability is about producing and managing content. It may include creating drafts, editing owned content, uploading approved media, or moving content into a review state.
Governance control is about approvals and policy enforcement. It may include the right to approve publication for regulated content, the ability to reject changes that bypass required review, or oversight of sensitive content categories.
Technical administration is about platform operation. It may include configuration management, content model changes, deployment coordination, and environment-level control.
These should not collapse into one broad privileged role unless there is a very strong reason. When they do, two problems usually follow.
The first is operational confusion. Business users gain technical powers they do not need, while technical teams become informal publishing approvers because they hold broad access.
The second is governance weakness. A platform cannot demonstrate meaningful separation of duties if the same small set of users can edit content, approve content, alter workflows, and override controls.
A more resilient model defines permissions across these layers explicitly. Not every organization needs strict four-eyes review on every content type. But every organization benefits from knowing which powers are editorial, which are governance-related, and which are administrative.
Workflow patterns for regional, legal, medical, or compliance review layers
Enterprise workflow design becomes much easier when permissions architecture is treated as a companion to workflow, not a substitute for it.
The key principle is that workflow states represent approval logic, while permissions determine who can move content through that logic. If the permissions model is unclear, workflow becomes overloaded with business exceptions. If workflow is unclear, permissions become too broad in order to compensate.
Several patterns commonly appear in enterprise Drupal publishing:
Regional publishing with central standards
A central team defines content standards and platform guardrails. Regional teams create and revise local content. Publication rights may remain regional for low-risk content, while some shared sections require central review.
In this pattern, permissions should distinguish between local editorial autonomy and central governance authority. The architecture should avoid forcing all regions into the same approval path when risk levels differ.
Conditional compliance review
Some content types or categories need legal, medical, or regulatory review. Others do not.
This is where role design needs discipline. The answer is usually not to grant compliance teams broad editorial rights across the platform. Instead, permissions should support targeted review responsibilities tied to content classes or approval states. The goal is controlled participation in publishing, not generalized editing power.
Shared services with delegated ownership
In platform consolidation programs, a shared digital team may support many business units. The business units own their content outcomes, but the platform team owns standards, architecture, and release integrity.
Here, the permissions model should preserve that boundary. The shared team can enable and govern publishing without silently becoming the operational owner of every publishing decision.
Across all of these patterns, the architecture should answer a basic question clearly: who is accountable for a piece of content at each stage of its lifecycle?
How to redesign permissions without freezing publishing operations
Many organizations know their permissions model is flawed but delay redesign because they fear disruption. That concern is reasonable. Permissions changes can interrupt critical publishing operations if approached as a big-bang cleanup.
A safer approach is phased and architectural.
Start with discovery, not role editing. Review existing roles, assigned permissions, workflow states, content types, and actual publishing behaviors. The important word is actual. Many enterprise platforms have an intended governance model and a separate operational reality.
Then identify the highest-risk mismatches, such as:
- users with production publishing rights outside their business responsibility
- approval steps that exist in policy but not in workflow enforcement
- administrative access used for routine editorial tasks
- duplicated roles that represent the same function in slightly different ways
From there, define a target permissions model based on capabilities and control boundaries. This is usually easier to implement if it is broken into layers described in Drupal governance architecture:
- core editorial roles that are consistent across the platform
- governance roles used only where approval control is required
- technical roles reserved for platform administration and release operations
- content-domain or regional variations introduced only where business need is real and sustained
Migration should be incremental. Platform teams can often stabilize the most sensitive content domains first, especially where compliance or brand risk is highest. Lower-risk areas can move later if necessary.
It is also important to plan for transitional coexistence. For a period, the old and new models may need to run in parallel while teams are remapped and responsibilities are clarified. That is acceptable if the transition has explicit deadlines and ownership.
Auditability, least privilege, and release discipline
A mature permissions architecture is not just easier to manage. It is easier to trust.
Auditability improves when roles have clear purpose and when workflow transitions align with business controls. Instead of asking whether a user had broad access, reviewers can assess whether the user had the specific authority required for a defined task.
Least privilege also becomes more practical. In weak models, least privilege is often treated as a security slogan that delivery teams cannot afford. In stronger models, it becomes an operational design principle. Users get the narrowest permissions that support their actual publishing responsibility.
Release discipline matters as well. In enterprise Drupal environments, permissions architecture should not be changed casually in production as an isolated admin action whenever a new exception appears. Changes to roles, workflow behavior, and governance controls should follow the same disciplined release thinking applied to other parts of the platform.
That does not mean every permission adjustment requires heavy process. It means the organization should know:
- who can authorize permissions changes
- how changes are reviewed for governance impact
- how exceptions are documented and retired
- how role definitions are kept aligned with operating model decisions
Without that discipline, permission sprawl will eventually return even after a successful cleanup.
A reference checklist for platform teams
For enterprise teams reviewing their current model, the following checklist is a useful starting point.
- Are roles based on stable responsibilities rather than inconsistent job titles?
- Can you clearly separate editorial work, governance approvals, and technical administration?
- Do workflow transitions reflect real approval obligations for different content risk levels?
- Are regional or business-unit variations intentional, limited, and documented?
- Can you explain why each role exists and which control it represents?
- Do any users rely on administrator-level access for routine publishing tasks?
- Are permissions changes governed with the same care as other platform controls?
- Can the platform demonstrate who is authorized to publish sensitive content and why?
- Is there a plan to remove legacy roles and temporary exceptions?
If the answer to several of these is no, the problem is probably architectural rather than procedural.
A good Drupal permissions model does not try to encode every organizational nuance into endless role variations. It creates a controlled framework where publishing responsibility, governance oversight, and technical administration are distinct, understandable, and scalable.
Drupal governance
Pressure-test your editorial permissions architecture
Identify where roles, workflows, and approval boundaries create publishing risk in multi-team Drupal environments.
That is the shift enterprise teams need to make. When permissions architecture reflects the real operating model, workflow becomes clearer, audits become easier, and publishing can scale without relying on informal workarounds. In a multi-team Drupal platform, that is what turns permissions from a source of risk into a foundation for reliable delivery, as seen in large-scale Drupal multisite modernization and governance-ready publishing workflows.
Tags: Drupal, Enterprise CMS, Drupal editorial permissions architecture, Drupal workflow governance, enterprise Drupal permissions, multi-team publishing controls