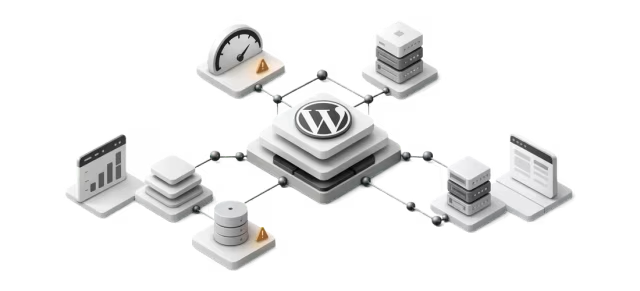
Enterprise campaign peaks create a specific kind of pressure on WordPress platforms. The challenge is not simply handling more visits. It is handling bursty demand, preserving frontend responsiveness, protecting editorial operations, and keeping recovery paths simple if production behavior diverges from expectations.
For CTOs, SRE leads, and platform engineers, wordpress infrastructure readiness should be treated as a launch discipline rather than a last-minute infrastructure check. The goal is to define what “ready” means in operational terms, test that posture before the campaign window, and create clear rollback criteria for when assumptions no longer hold.
Check if your stack is ready for campaign trafficRun a quick WordPress Health CheckDefine readiness in terms of business risk and service objectives
Infrastructure readiness starts with a shared definition of success. For campaign events, the question is not whether the platform can survive traffic in a technical sense. The question is whether it can sustain the business experience expected during peak attention.
That usually means aligning on a small set of practical objectives:
- public pages remain fast enough to protect conversion and discovery
- origin systems remain stable under elevated concurrency
- cache behavior absorbs the majority of anonymous traffic
- publishing and approval workflows remain usable for editors
- incident signals are visible early enough to intervene before widespread degradation
This is where service-level thinking matters. Even if a team does not run a formal SLO program, it should define a few launch-critical indicators ahead of time. Typical examples include:
- acceptable ranges for page response time at the CDN and origin layers
- guardrails for error rate and saturation on application nodes
- tolerable queue depth for PHP workers or request handling pools
- database latency thresholds for core read and write paths
- Core Web Vitals targets for campaign landing pages under realistic traffic mix
- admin responsiveness targets for editorial tasks that may continue during launch
The main value of these targets is decision quality. Without them, readiness reviews tend to become subjective. With them, teams can identify whether they are capacity-constrained, cache-constrained, code-constrained, or simply missing observability.
Assess runtime bottlenecks before adding capacity
A common mistake in a wordpress scaling strategy is to scale infrastructure before understanding where requests actually spend time. More nodes can help, but only if the bottleneck lives in compute capacity. If the real issue is slow cache fill, serialized admin actions, database contention, or external API latency, horizontal scaling alone will not solve the launch risk.
Start by mapping the main request classes:
- anonymous page views for campaign landing pages
- authenticated admin traffic from editors, marketers, and approvers
- AJAX or API requests used by theme features or plugins
- scheduled jobs such as cron-triggered tasks, imports, or cache warmers
- webhook or integration traffic from marketing and analytics systems
Each class behaves differently under pressure. Anonymous traffic should mostly be served from the edge or a full-page cache. Authenticated traffic usually reaches origin and puts pressure on PHP execution, session handling, and database reads. Background jobs can compete for the same compute and database resources needed for user-facing requests if isolation is poor.
A practical runtime review should answer a few direct questions:
- How many concurrent dynamic requests can the application layer handle before latency rises sharply?
- What happens when PHP workers are exhausted?
- Are autoscaling decisions fast enough for a campaign spike, or does the system rely on pre-scaling?
- Are background processes isolated from web-serving capacity?
- Are third-party calls on the critical path bounded by timeouts and fallbacks?
For enterprise WordPress, pre-scaling is often safer than relying entirely on reactive autoscaling. Campaign traffic can ramp too quickly for cold capacity to become useful in time. If autoscaling is part of the design, validate scale-out trigger sensitivity, warm-up times, and load balancer behavior under rapid changes.
Evaluate database behavior as a first-class launch dependency
WordPress sites under campaign pressure often fail at the database layer before they fail anywhere else. That is especially true when plugins generate repetitive reads, cache keys are inconsistent, or administrative workflows produce bursts of writes during launch windows.
Database readiness is not just about average utilization. It is about query shape, contention, and recovery under uneven traffic.
Pressure-test WordPress performance before launch day
Surface cache gaps, origin bottlenecks, and database risk before campaign traffic exposes them.
- Check cache readiness
- Spot origin bottlenecks
- Validate peak resilience
Review the following areas:
- slow or high-frequency queries on landing pages and high-traffic templates
- excessive autoloaded options or oversized object payloads
- expensive
WP_Querypatterns, especially on uncached archive or search experiences - plugin-driven metadata queries without effective indexing or caching
- write-heavy behaviors from logs, sessions, carts, personalization, or marketing integrations
- replication lag risk if the architecture separates reads and writes
The most useful pre-launch exercise is to identify which queries matter during peak traffic and whether they are expected to hit memory caches, object caches, or the primary database. If teams cannot answer that confidently, they are effectively launching on assumption.
For editorial continuity, also test backend operations that are easy to overlook:
- saving and updating campaign pages
- media uploads and image processing
- preview generation
- scheduled publishing
- cache purges triggered by content updates
A platform can appear healthy from a frontend perspective while editors experience severe latency. That becomes a serious operational problem during active campaigns when messaging, disclaimers, or creative assets may need to change quickly.
Review caching and edge behavior as a system, not a feature
For most campaign events, wordpress caching infrastructure is the single biggest determinant of stability. But caching only works as a protection layer when teams understand the complete cache path from browser to CDN to reverse proxy to application and object cache.
The review should be holistic.
Full-page caching
Anonymous campaign traffic should ideally be served from a full-page cache at the edge or a high-performance reverse proxy. The key question is not whether caching exists, but whether the campaign URLs actually qualify for it.
Check for common cache blockers:
- cookies set too broadly across the site
- query parameters that unnecessarily bypass cache
- personalization logic on pages that should remain static for most users
- plugin behavior that marks responses as uncacheable
- inconsistent cache headers between application and edge
It is also important to validate cache key strategy. If every trivial variation creates a separate cache object, hit ratio can collapse during peak traffic and shift load back to origin.
Object caching
Persistent object caching can reduce repeated database reads, but its benefits depend on disciplined usage. Teams should understand which application paths rely on object cache, how keys are invalidated, and what happens if the cache is cold or partially evicted.
A cache tier that performs well during normal traffic can still fail operationally during launch because of:
- aggressive invalidation after content deployment
- insufficient memory for hot objects
- noisy-neighbor patterns from unrelated jobs or workloads
- uneven distribution of large objects
CDN and edge configuration
Enterprise campaign traffic usually reaches the edge first, so edge readiness deserves the same attention as application readiness.
Validate:
- origin shielding or equivalent protections where appropriate
- request collapsing behavior during cache misses
- rate limiting or bot controls for abusive patterns
- image optimization and compression rules
- stale content behavior when origin latency rises
- header forwarding rules that may fragment cacheability
In practice, many launch-day incidents are not caused by inadequate raw infrastructure. They are caused by an edge configuration that unintentionally routes too much demand to origin.
Plan capacity around traffic shape, not a single peak number
Campaign preparation often begins with a projected traffic peak. That is useful, but incomplete. Two campaigns with the same peak traffic can produce very different infrastructure outcomes depending on how traffic arrives.
Teams should model:
- burst intensity over short windows
- geographic concentration and its CDN implications
- ratio of new visitors to returning visitors
- share of mobile traffic and network-constrained users
- landing-page concentration versus multi-page browsing depth
- proportion of anonymous to authenticated traffic
This matters because systems behave differently under bursty concurrency than under smooth growth. A sudden influx can trigger synchronized cache fills, database hot spots, and saturation before autoscaling has time to respond.
For campaign traffic planning, it is usually better to think in terms of traffic envelopes:
- expected case
- high-confidence peak case
- stress case used for rehearsal and contingency validation
That framing gives teams a better basis for pre-scaling, failover planning, and launch staffing.
Rehearse load using production-like behavior
A load test is only useful if it resembles the conditions that matter. Synthetic tests that hit one page repeatedly with perfect cacheability can confirm that the CDN works. They cannot confirm that the overall platform is launch-ready.
A useful rehearsal should include:
- the actual high-priority campaign URLs
- realistic header and cookie behavior
- a representative mix of cache hits and misses
- origin requests for authenticated or semi-dynamic workflows where relevant
- realistic third-party dependencies if they are on the request path
- enough duration to expose saturation, memory pressure, and recovery behavior
The test should also be staged in phases.
Phase 1: Baseline
Establish normal performance and resource patterns with current production-like configuration. This creates the comparison point for later tuning.
Phase 2: Peak simulation
Increase load toward the expected campaign envelope while monitoring response time, error rate, worker utilization, database latency, cache hit ratio, and edge-origin request volume.
Phase 3: Stress and failure behavior
Push beyond the expected peak to identify where latency bends, errors begin, and which component becomes the dominant bottleneck. This helps define rollback criteria and operational thresholds.
Phase 4: Recovery
Reduce traffic and observe whether the platform recovers quickly or remains degraded because of queue buildup, exhausted workers, or unhealthy cache state.
The point is not to produce an impressive top-line number. It is to understand how the system behaves before, during, and after stress.
Instrument observability around launch decisions
Readiness depends on visibility. Teams need dashboards and alerts that reflect the campaign architecture rather than a generic infrastructure view.
At minimum, instrument these layers:
- CDN or edge request rate, cache hit ratio, origin fetches, and status code distribution
- load balancer or ingress latency and backend health
- application node CPU, memory, worker saturation, restart patterns, and request latency
- PHP or runtime execution time, queue depth, and timeout frequency
- database connection usage, query latency, lock behavior, and replication health where applicable
- object cache memory pressure, evictions, and command latency
- Core Web Vitals and real-user performance for launch-critical pages
- admin workflow latency for editing and publishing operations
During campaign windows, aggregate these into a launch-focused dashboard rather than forcing responders to pivot across disconnected tools. The dashboard should support a few practical decisions:
- Is the edge absorbing load as designed?
- Is origin saturation building?
- Is performance degradation affecting users or only internal operations?
- Are content changes making cache behavior worse?
- Has the platform crossed a threshold that justifies traffic shaping, feature reduction, or rollback?
Establish pre-launch checkpoints
Readiness improves when checkpoints are explicit and signed off before launch day. A useful checkpoint list should be short enough to use and specific enough to matter.
A practical pre-launch checklist can include:
- critical landing pages confirmed cacheable for anonymous users
- cache headers and edge rules validated for campaign URLs
- application capacity pre-scaled or reserved for expected traffic windows
- background jobs reviewed, deferred, or isolated where necessary
- top database queries reviewed for high-traffic templates
- plugin and theme changes frozen or tightly controlled near launch
- monitoring dashboards prepared and on-call routing confirmed
- test results reviewed against defined readiness thresholds
- editorial workflows validated under production-like conditions
- fallback content and degraded-mode options documented
For complex launches, include explicit ownership for each checkpoint. A checklist with no named owners tends to become informational rather than operational.
Define rollback criteria before the campaign starts
One of the most overlooked infrastructure controls is a clear rollback model. Teams often discuss rollback in application deployment terms, but campaign resilience also requires operational rollback criteria.
Define in advance what conditions trigger action. Examples may include:
- sustained origin error rate above an agreed threshold
- materially degraded cache hit ratio that does not recover after intervention
- database latency rising beyond safe operating range for a sustained period
- frontend performance degradation on key landing pages that threatens business outcomes
- admin or publishing workflows becoming unusable during active campaign management
Rollback does not always mean reverting code. It can also mean stepping back to a safer operating mode, such as:
- disabling nonessential dynamic features
- pausing high-cost integrations
- reverting edge rules that fragment cache
- restoring previous infrastructure configuration
- serving a simpler campaign template with stronger cacheability
- delaying noncritical content changes until load stabilizes
The important point is that rollback options should be prepared, tested where possible, and tied to observed signals. In a live event, teams rarely have time to invent a safe rollback path from scratch.
Protect editorial operations during peak windows
Enterprise campaigns often require real-time adjustments after launch. Legal copy changes, creative swaps, regional updates, and navigation changes may all need to happen while public traffic is elevated.
That makes editorial resilience part of infrastructure readiness.
Consider safeguards such as:
- separating admin capacity from public-serving capacity where architecture permits
- controlling who can publish during peak windows
- using scheduled releases carefully to avoid synchronized cache invalidation
- warming cache after major content changes
- validating media workflows so image processing does not compete with user traffic
A platform that protects public response times but blocks business users from making essential updates is not fully ready.
Common anti-patterns that undermine readiness
Even mature teams can miss avoidable issues when launch timelines compress. A few patterns show up repeatedly:
- treating average traffic as the planning basis instead of burst behavior
- assuming all campaign pages are cacheable without validating cookies and headers
- load testing only the homepage or only warm-cache scenarios
- ignoring backend and editorial workflows during peak planning
- introducing plugin or template changes too close to launch
- relying on autoscaling without validating warm-up and dependency limits
- monitoring infrastructure health without tying it to user experience and business paths
These issues are usually fixable, but only if they are surfaced early enough to inform launch decisions.
A practical readiness model for campaign teams
For most enterprise WordPress programs, the most effective model is straightforward:
- define launch-critical user journeys and service objectives
- identify the main request classes and bottlenecks across runtime, cache, and database layers
- validate cacheability and edge behavior for real campaign paths
- rehearse production-like load and observe both saturation and recovery
- establish pre-launch checkpoints, named owners, and rollback criteria
- monitor launch using a focused dashboard tied to decision thresholds
This creates a repeatable readiness process rather than a one-time fire drill.
WordPress can support significant campaign demand when the platform is designed and operated with that demand in mind. But readiness is rarely the result of one tuning change or one infrastructure upgrade. It comes from reducing ambiguity across the entire delivery path: what should be cached, what must stay dynamic, where the bottlenecks are, how much headroom exists, and what the team will do if production behavior drifts from plan.
WordPress performance
See where campaign traffic could strain your platform
Use the Health Check to uncover cache fragmentation, worker saturation, slow queries, and launch-day performance risks across your WordPress stack.
If a campaign team can answer those questions clearly before launch, it is usually in a much stronger position to absorb traffic spikes without sacrificing Core Web Vitals, origin stability, or editorial control.
Tags: WordPress, Infrastructure, Performance Engineering, Scalability, SRE, Enterprise Platforms