Enterprise teams often reach for WordPress because it is familiar, editor-friendly, and flexible. That same flexibility becomes a liability when a company needs to support multiple brands, regions, business units, or campaign teams on one platform. Without a clear reference architecture, shared code starts leaking across brands, governance becomes inconsistent, release risk grows, and platform performance degrades over time.
Check your WordPress architecture baselineRun a quick WordPress Health CheckA useful wordpress reference architecture does not try to eliminate variation. It defines where variation is allowed, how shared capabilities are consumed, and which controls protect reliability. For CTOs, enterprise architects, and engineering managers, the goal is usually straightforward: enable brand autonomy where it creates value, while centralizing the parts that improve quality, speed, security, and maintainability.
What a reference architecture should solve
For a multi-brand WordPress platform, the architecture should answer a few recurring questions:
- Which layers are shared across every brand?
- Which capabilities can a brand team configure without affecting others?
- Which capabilities require platform-level governance?
- How are releases coordinated when some assets are shared and others are local?
- Who owns data models, integrations, and operational controls?
If those answers are unclear, delivery tends to fragment. Teams may still ship, but they do so through exceptions, duplicated effort, and rising regression risk.
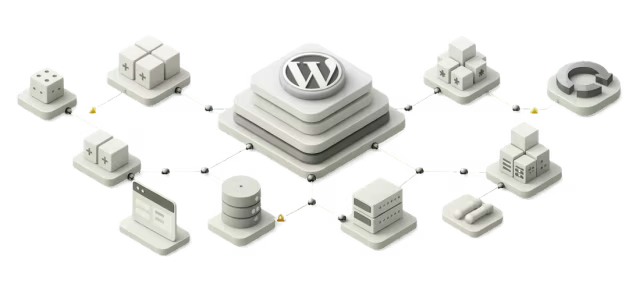
The core architectural model
A practical wordpress platform architecture usually works best when organized into four layers:
- Infrastructure and runtime layer
- Platform services and shared tooling layer
- Experience and component layer
- Brand implementation layer
The point of separating these layers is not diagram purity. It is to create stable contracts. Once teams know which layer they are changing, they can understand blast radius, approval requirements, testing depth, and release sequencing.
Layer 1: Infrastructure and runtime
This layer contains the hosting model and operational baseline:
- container or VM strategy
- web tier and PHP runtime conventions
- CDN and caching policy
- object cache and page cache strategy
- media storage approach
- database topology
- secrets management
- observability and incident tooling
- backup and disaster recovery controls
In multi-brand delivery, this layer should be heavily standardized. Brand teams rarely gain meaningful value by selecting their own caching rules, log pipelines, or backup patterns. Those choices are better treated as platform concerns.
A good rule is that infrastructure decisions should expose a small set of approved configuration options rather than unlimited freedom. For example, brands may choose from pre-approved cache behaviors for authenticated versus anonymous traffic, but they should not create custom infrastructure patterns that the platform team cannot support consistently.
Trade-off: Strong standardization reduces operational entropy, but it can frustrate teams with unusual requirements. The architecture should therefore include an exception path, but one that is explicit, reviewed, and time-bounded.
Layer 2: Platform services and shared tooling
This is the layer where governance and scale are often won or lost. Typical shared services include:
- identity and access controls
- CI/CD pipelines
- code quality enforcement
- dependency management standards
- design token distribution
- image optimization services
- search services
- analytics instrumentation standards
- security scanning
- content migration utilities
For enterprise WordPress, this layer should be designed as a managed platform capability rather than a loose toolkit. In other words, it is not enough to publish reusable scripts and hope teams consume them correctly. Shared tooling should be integrated into the default workflow.
For example, if every brand site depends on the same deployment pipeline, then release controls such as automated testing, artifact versioning, and rollback procedures can be applied consistently. If each brand invents its own pipeline, platform governance becomes mostly advisory.
Trade-off: Central pipelines increase consistency, but they can slow teams when approval steps are too broad. A mature design uses policy-based automation so the pipeline enforces known rules while avoiding unnecessary manual gates.
Layer 3: Shared experience and component system
This is usually the most visible part of a wordpress reference architecture. It includes the reusable building blocks used across brands:
- shared theme framework or frontend shell
- approved Gutenberg blocks or custom block library
- design system components
- layout primitives
- accessibility standards
- navigation patterns
- SEO metadata conventions
- content model patterns
The most important principle here is to separate shared components from shared presentation decisions. Brands often should reuse the same component contract without being forced into identical visual execution.
A strong component contract typically defines:
- functional behavior
- data requirements
- accessibility requirements
- analytics hooks
- performance expectations
- extension points
- version compatibility rules
A brand implementation can then apply local styling, copy conventions, and approved layout variations without rewriting the underlying capability.
This is how shared component governance becomes practical instead of restrictive. Governance is not just a central team saying no. It is a system of versioned, documented contracts that let brands move quickly within defined boundaries.
Layer 4: Brand implementation boundary
Each brand needs space for legitimate differentiation. That usually includes:
- visual identity and theming
- editorial taxonomies unique to the brand
- market-specific content workflows
- campaign-specific landing page behavior
- optional integrations approved for that business unit
- feature flags for incremental rollout
The mistake many organizations make is letting this boundary expand until the shared platform becomes irrelevant. A brand boundary should be broad enough to support customer-facing differentiation, but narrow enough to prevent reinvention of platform concerns.
A useful test is this: if two brand teams solve the same engineering problem differently, would that divergence improve customer outcomes or simply increase support overhead? If it is mostly overhead, the capability should probably move into the shared layer.
Defining shared versus local ownership
A multi-brand platform becomes easier to govern when ownership is explicit. One workable model is:
Platform team owns:
- runtime and infrastructure standards
- core security controls
- CI/CD templates and release guardrails
- shared component library
- cross-brand design tokens
- observability baseline
- common plugin evaluation and approval
Brand team owns:
- brand theme configuration and approved overrides
- content operations
- campaign execution
- local navigation and page composition
- approved integration configuration
- brand-level backlog prioritization
Joint ownership areas:
- content model evolution
- analytics event design
- personalization strategy
- search relevance tuning
- roadmap decisions affecting multiple brands
Joint ownership is where ambiguity tends to create delays. The architecture should therefore define not just owners, but decision rights. Who proposes a schema change? Who approves it? Who tests downstream impact? Who communicates release readiness?
Architectural contracts that reduce friction
Reference architectures are most useful when they define contracts that teams can design against. In a WordPress environment, the most important contracts often include the following.
See where your platform model creates delivery risk
Assess shared layers, ownership boundaries, and release controls before multi-brand complexity spreads.
- Audit shared platform layers
- Spot ownership gaps fast
- Check release control maturity
Component contract
Every shared block or module should document:
- input fields and validation rules
- rendering behavior
- design token usage
- accessibility requirements
- analytics events
- caching expectations
- backward compatibility policy
This reduces the temptation for local teams to fork components just to handle edge cases that should have been modeled as extensions.
Content model contract
Where multiple brands share publishing workflows or integrations, content types should have clearly versioned schemas. That does not mean every brand must have identical content structures. It means shared integrations should target stable interfaces.
For example, if downstream systems consume article metadata, promo modules, or author records, the architecture should define which fields are canonical and which are optional or brand-specific.
Integration contract
External systems should not integrate directly with ad hoc theme logic. They should integrate with a defined application boundary, such as:
- a service wrapper
- a domain plugin
- a platform API adapter
- a queue or event interface where appropriate
This matters because integration logic is one of the first places multi-brand platforms become difficult to upgrade. When every brand implements API calls differently, even minor vendor changes create broad regression risk.
Operational contract
The platform should define baseline expectations for:
- logging and tracing
- uptime monitoring
- rollback procedure
- support escalation path
- incident classification
- performance budgets
Without an operational contract, teams may technically share a platform while functioning as separate unmanaged estates.
Deployment and release orchestration
Release quality is where reference architecture becomes real. Enterprise teams do not only need reusable code. They need a delivery model that can support shared assets and brand-specific change at the same time.
A practical release model often uses three release streams:
- Platform releases for shared infrastructure, approved plugins, shared libraries, and runtime changes
- Component releases for versioned UI blocks and cross-brand experience modules
- Brand releases for local configuration, content model use, campaign features, and theming
This separation helps teams avoid one giant release train while still preserving control.
A common pattern is:
- platform changes move on a planned cadence
- component updates are versioned and adopted by brands based on compatibility windows
- brand changes deploy independently within approved policy constraints
That model works well when backward compatibility is treated seriously. If shared components can introduce breaking changes without discipline, brand teams will pin versions indefinitely, and the platform will fragment.
Trade-off: Strict semantic versioning and compatibility support require platform maturity. The upside is lower upgrade risk. The downside is more investment in release engineering and documentation.
Recommended release controls
For enterprise governance, the following controls are usually worth implementing:
- automated tests at unit, integration, and critical journey levels
- visual regression checks for shared components
- contract testing for integrations
- environment promotion rules with traceable approvals
- artifact versioning and changelogs
- canary or phased rollout where traffic patterns justify it
- rollback paths tested before major shared releases
Not every brand release needs the same depth of scrutiny. The architecture should classify change types by risk. A copy-only content update should not pass through the same approval model as a shared authentication change.
Data and integration ownership
Data ownership becomes especially important when multiple brands share customer, product, campaign, or search data. WordPress should not become the accidental system of record for domains it is not designed to govern.
A practical model is:
- WordPress owns editorial composition and publishing state
- upstream business systems own canonical product, account, or transactional data
- shared services own transformation or aggregation where multiple brands consume the same source
- each integration has a named owner for schema changes, credential rotation, failure handling, and SLA expectations
This matters because many platform failures are not pure application failures. They are failures of unclear ownership between content, application, and enterprise data teams.
When designing integration patterns, use the simplest pattern that matches business criticality:
- synchronous API calls for low-latency, low-complexity needs
- scheduled synchronization for less time-sensitive reference data
- event-driven patterns where multiple downstream consumers rely on content state changes
Trade-off: Event-driven integration can improve decoupling, but it adds operational complexity. If the estate is not ready to monitor and govern asynchronous flows properly, a simpler polling or scheduled sync pattern may be safer.
Performance and governance are linked
Performance issues in a multi-brand WordPress platform are rarely caused only by traffic volume. They often come from inconsistent implementation decisions across brands.
Examples include:
- custom blocks bypassing platform asset loading rules
- local plugins introducing duplicate queries or external dependencies
- theme overrides breaking cache assumptions
- analytics scripts added outside approved governance
This is why performance should be treated as an architectural contract, not a post-launch optimization task. Shared standards should define:
- frontend asset budgets
- image handling rules
- third-party script approval process
- server-side rendering or caching expectations
- query profiling thresholds
Brand freedom is still possible, but it should operate inside measurable limits.
A practical operating model
A reference architecture becomes sustainable when paired with a clear operating model. In most enterprise contexts, that means:
- a platform architecture board for shared decisions
- documented standards for exceptions and waivers
- versioned component and plugin catalogs
- release notes visible to both platform and brand teams
- scheduled architecture reviews for high-impact changes
- shared backlog intake for capabilities affecting more than one brand
The key is not bureaucracy for its own sake. The point is to make important platform decisions explicit before they become expensive to reverse.
Architecture review checklist
When reviewing a proposed change to a multi-brand WordPress platform, this checklist helps reveal whether the change fits the reference architecture:
- Does the change belong in the shared layer or the brand layer?
- Is there a documented reason if the capability is not reusable?
- What contract does the change introduce or modify?
- Does it create a new dependency on a plugin, vendor, or external service?
- Who owns the integration and operational support model?
- What is the release path, and what is the rollback path?
- Does it affect performance budgets or caching behavior?
- Does it require schema changes across brands?
- Is backward compatibility defined for existing consumers?
- Are analytics, accessibility, and security requirements included from the start?
- Can the change be tested in isolation and in shared platform contexts?
- Does the change create a precedent that will be hard to govern later?
This checklist is especially useful for stopping local optimizations from becoming platform liabilities.
Common failure patterns to avoid
There are a few predictable ways these programs drift off course:
- treating shared code as a dumping ground for unresolved brand requirements
- allowing unrestricted plugin adoption by local teams
- skipping versioning for shared components
- letting integrations attach directly to theme or page-level implementations
- centralizing every decision, which pushes teams toward shadow delivery patterns
- over-federating the platform, which eliminates reuse and weakens governance
A good reference architecture is not purely centralized or purely decentralized. It is deliberately layered.
Final recommendation
The best wordpress reference architecture for multi-brand platforms is the one that makes autonomy safe. It standardizes infrastructure, tooling, operational controls, and reusable component contracts. It also gives brands enough space to express local identity, support business-specific workflows, and ship at an appropriate pace.
If you are designing or resetting a wordpress platform architecture, start by defining boundaries rather than technologies. Decide what must be shared, what may vary, and what release controls protect the whole estate. Once those contracts are explicit, WordPress can support multi-brand delivery without fragmenting governance, performance, or release quality.
Multi-brand WordPress architecture
Validate the platform decisions behind every brand rollout
Use the Health Check to uncover weak contracts, governance gaps, and scaling risks across your WordPress estate.
That is the real value of a reference architecture: not a static diagram, but a working model for scaling delivery with less friction and fewer surprises.
Tags: wordpress reference architecture, Architecture, multi-brand wordpress platform, wordpress platform architecture, shared component governance