Is Your Enterprise Drupal Platform Truly Secure?
Many Drupal platforms accumulate risk over time as teams ship features, add contributed modules, and evolve infrastructure without consistent security engineering oversight. Outdated dependencies, configuration drift, and permission sprawl can create exploitable gaps—often across multiple environments and deployment workflows. Even small misconfigurations in roles, file permissions, administrative endpoints, or caching layers can lead to data exposure, service disruption, or difficult-to-trace integrity issues.
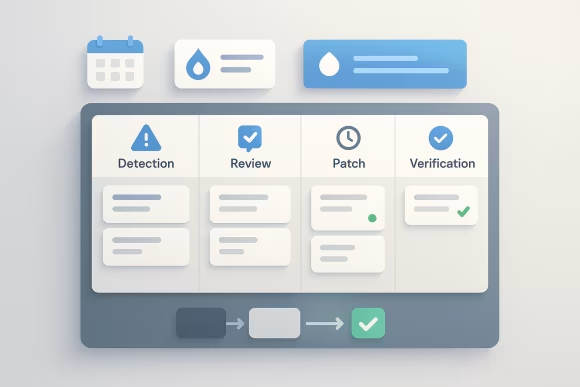
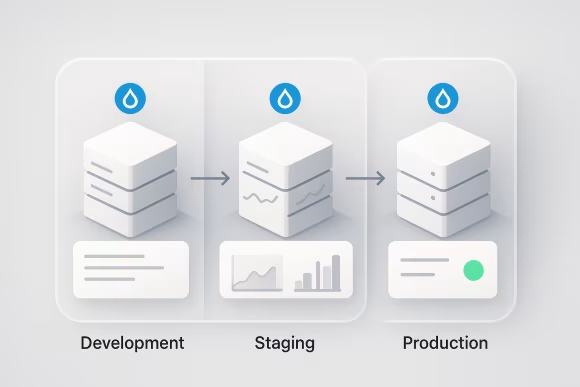
In enterprise settings, security challenges are rarely isolated to application code. Fragmented ownership between development, operations, and compliance stakeholders can result in inconsistent controls, incomplete logging, and unclear accountability for patching and vulnerability management. When security updates are handled reactively, organizations face delivery bottlenecks, rushed releases, and higher regression risk—especially when changes are not validated in controlled staging environments.
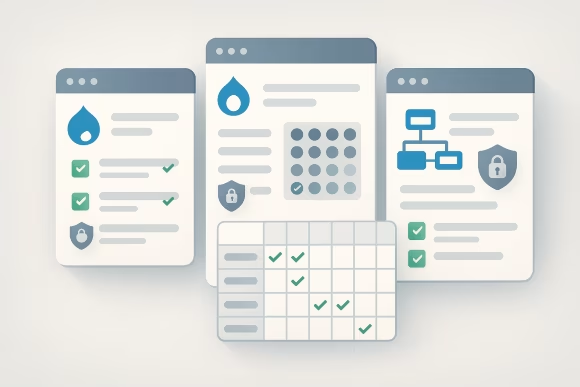
For regulated industries, the operational burden increases further: documentation gaps, weak governance processes, and unclear data-handling practices can translate into audit findings and compliance exposure. Without a structured approach to Drupal compliance expectations (including GDPR and HIPAA-aligned architecture considerations), teams may struggle to demonstrate control effectiveness, maintain evidence, and reduce ongoing operational risk.
 [01]
[01]